According to data from the Bee Informed Partnership, a national collaboration of leading research labs and universities in agricultural science, managed honeybee populations declined by nearly 40% between Oct. 1, 2018 and April 1, 2019. This is a 7% greater decline compared to the same timeframe during the previous winter.1
Scientists are examining different environmental factors such as the increased use of pesticides and the use of chemicals in agriculture as causes for the rapid decline in global honeybee numbers.
Recent research conducted by my team and I revealed a potentially key reason for the decline in honeybee populations as a result of Nosema ceranae (N. ceranae), a prevalent infection in adult honeybee populations. My team established a link between N. ceranae-infected honeybee colonies and changes in pheromone levels, which in turn, may have a social impact on communication in honeybee colonies.
Moreover, the significant decline in the global honeybee population is likely to be driving an increase in fraudulent honey, meaning that both governments and regulators need to invest in the latest technology to test honey products for authenticity, nutritional values and safety.
The Significance of Honey in Our Global Diet and the Problem at Hand
Honey has been a part of our diet for the past 8,000 years, and with numerous health benefits in addition to having a favorable taste, it is one of the most popular foods across the globe.2
Honeybees produce honey from the nectar of flowering plants, and they are considered a “keystone species” since one-third of human food supply depends on pollination by honeybees.3The species is responsible for pollinating numerous fruit, nut, vegetable and field crops such as apples, almonds, onions and cotton.
The increase of pesticides and chemicals in the environment has been cited as a reason for the decline in bee populations, which has occurred in Western European countries such as France, Belgium, Germany, the UK, Italy, Spain, and the Netherlands, as well as countries such as the United States, Russia and Brazil.4 In fact, the number of honeybee colonies in Europe fell by an average of 16 per cent over the winter of 2017–2018, according to findings published in the Journal of Apiculture Research.5
Global pesticide usage was predicted to increase to 3.5 million tons globally in 2020, which could mean that honeybee populations will continue to diminish at an exponential rate due to the increased use of pesticides.6
The Impact of Pesticides on Global Honeybee Populations
In 2019, a research project was initiated to explore the link between exposure to xenobiotic pesticides and increasing susceptibility to the N. ceranae infection in honeybee colonies, one of the most common infections in adult honeybee populations. The findings suggested that it is not the amount of pesticide exposure, nor a particular kind of pesticide exposure, but rather the number of exposure events from different xenobiotics that is associated with N. ceranae, which infected hives, thereby causing them to diminish.7
For discovery-based (non-targeted) exposome profiling of honeybee extracts, a gas chromatography/quadrupole time-of-flight mass spectrometer (GC/Q-TOF) was used. Additionally, spectral library searches and compound annotation were performed using the NIST 14, RTL Pesticides and the Fiehn Metabolomics libraries to provide efficient and timely research outputs.8
Expanding on this research further in 2021, a scientist’s team established a link between N. ceranae-infected honeybee colonies and changes in pheromone levels, which showed a potential impact on social communication in honeybee colonies. While it was concluded that further analysis is required, as research points to the real possibility that N. ceranae-infected honeybee colonies show increased alarm pheromones and may affect hive communication, which could ultimately, be a reason for the collapse of colonies.9
As N. ceranae is causing honeybee populations to dwindle worldwide, the decline in ‘real’ honey supplies is correspondent with an increase in ‘fake’ honey. Inauthentic honey products cause businesses and consumers to lose out, as ‘fake’ honey floods the market and makes producing ‘real’ honey more expensive.
Growth in Fake Honey
The global honey market has grown from 1.5 million tons produced annually in 2007 to more than 1.9 million tons in 2019 and the market is estimated to be worth $7 billion, however the decline in bee populations has led to an increase in honey adulteration to fill the global demand for honey.10
Declining supplies of authentic honey combined with the strong consumer demand for honey has driven significant adulteration of this product. Honey is considered to be one of the most adulterated foods after milk and olive oil, with every seventh jar of honey opened daily around the globe thought to be fake.11, 12 Consequently, legitimate honeybee keepers and business owners are forced to slash costs, which is problematic for those who depend on selling authentic honey.
To put into perspective the scale of the issue, the European agricultural organization, Copa-Cogeca noted that most honey imported from China into Europe is mixed with syrup.13 In 2018, the Honey Authenticity Project in Mexico commissioned tests for British supermarket honey products, and 10 out of 11 products failed the tests due to suspected sugar adulteration.14
While in the United States, it was recently reported that thousands of commercial beekeepers have taken legal action against the country’s largest honey importers and packers for allegedly flooding the market with hundreds of thousands of tons of “fake” honey.15 Furthermore, a recent workshop led by the South Africa Bee Industry Organization (SABIO) also conducted research on the impact of fraudulent honey, and the organization found that honey imports into South Africa have tripled to 6,000 tons a year, 60% of which come from China.16 As the demand for honey products stays robust but authentic honey supplies dwindle, the issue of counterfeit honey will continue to worsen.
Testing Methods to Identify Authentication
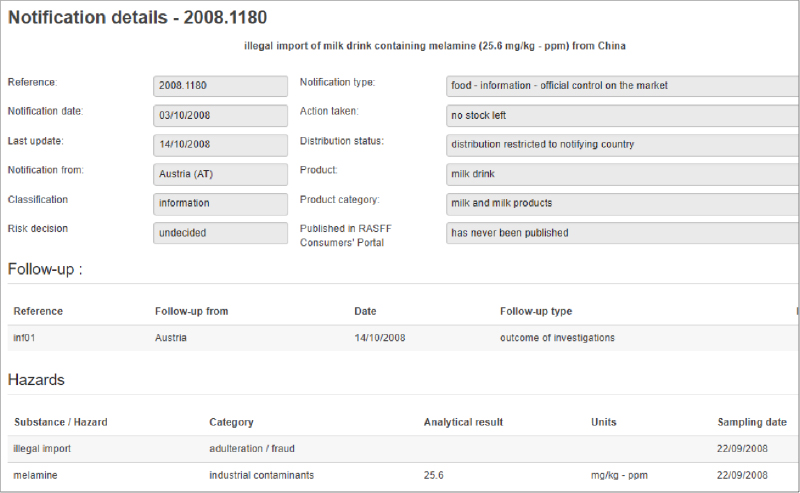
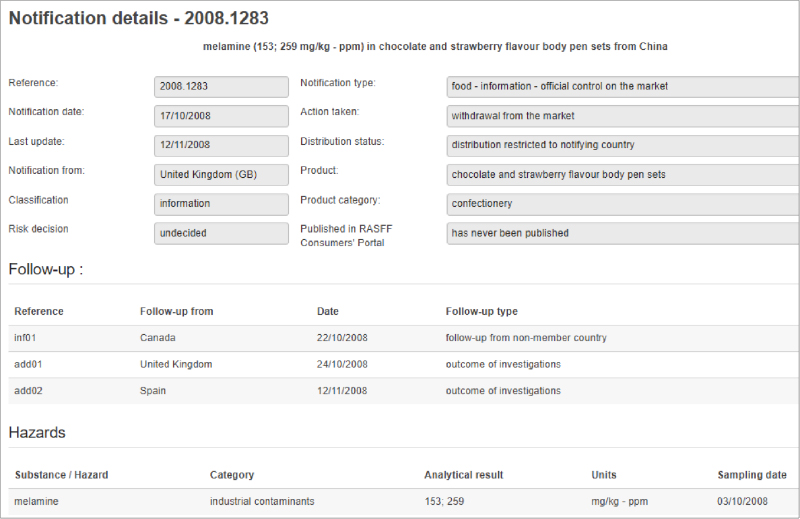
The issue of fraudulent food products like honey has driven governments to set up laws and departments dedicated to food integrity. Examples include FSMA, the UK National Food Crime Unit, Chinese Food Safety Law, and European Commission Food Integrity Project.
Food retailers often have contractual agreements with suppliers that require them to carry out authenticity testing of their ingredients, which can be carried out by third-party laboratories.17 Food adulteration can be identified via targeted and non-targeted testing and common testing methods include molecular spectroscopy solutions for ‘in the field’ screening and more in-depth laboratory analysis to determine quantities of ingredients.
Analytical instrument manufacturers have been working closely with governments to provide the latest methods to test the authenticity of honey products, as well as working with the Association of Official Agricultural Chemists (AOAC) on the development of both targeted and non-targeted standards for authenticity testing in milk, honey and olive oil.
Measuring contaminants is a key solution to identifying counterfeit honey and gas chromatographs are able to analyze and quantify the absence or presence of hundreds of pesticides in organic-labeled honey.18
Testing and analysis can be done using a range of analytical instrumentation such as solid phase microextraction followed by gas chromatography/mass spectrometry (SPME-GC/MS), inductively coupled plasma-mass spectrometry (ICP-MS), and gas/liquid chromatography/quadrupole time-of-flight (GC/Q-TOF and LC/Q-TOF). These instruments can be coupled with innovative software solutions for advanced data analysis.19
Future Research Must Continue
The spread of diseases such as N. ceranae, which have been shown to be aggravated by human-induced environmental factors, are decimating global honeybee populations, which in turn is negatively impacting ecosystems and humans, and the availability of authentic honey. This demise in authentic honey supplies is additionally fueling a rise in fake honey products, where consumers are misled into buying counterfeit honey.
Future research must continue to seek associations with environmental exposures effects on biological pathways and adverse health outcomes in honeybee populations, and in fact, novel environmental exposures have been found to be associated with seven of the top diseases known to affect honeybees. These putative associations must be validated with targeted follow-up studies to determine if they are causative factors in the decline of honeybee populations. If proven to be causative, scientists and policy makers can work together to mitigate these factors and hopefully reverse the global trend of honeybee colony decline.
References
- Loss & Management Survey, Bee Informed. Last accessed: June 2021
- Agilent.‘The Buzz around Fake Honey’. 2018. Last accessed: June 2021
- University of California – Berkeley. ‘Pollinators Help One-third Of The World’s Food Crop Production’. 2006. Last accessed: June 2021
- European Parliament. ‘What’s behind the decline in bees and other pollinators?’. 2021. Last accessed: June 2021
- Journal of Apiculture Research. ‘Loss rates of honeybee colonies during winter 2017/18 in 36 countries participating in the COLOSS survey, including effects of forage sources’. 2019. Last accessed: June 2021
- SN Applied Sciences. ‘Worldwide pesticide usage and its impacts on ecosystem’. 2019. Last accessed: June 2021
- PLOS ONE. ‘Honey bee (Apis mellifera) exposomes and dysregulated metabolic pathways associated with Nosema ceranae infection’. 2019. Last accessed: June 2021
- PLOS ONE. ‘Honey bee (Apis mellifera) exposomes and dysregulated metabolic pathways associated with Nosema ceranae infection’. 2019. Last accessed: June 2021.
- Royal Society Open Science. ‘Increased alarm pheromone component is associated with Nosema ceranae infected honeybee colonies’. 2021. Last accessed: June 2021
- Statista. ‘Global market value of honey 2019-2027’. 2021. Last accessed: June 2021
- Insider.com. ‘Honey is one of the most faked foods in the world, and the US government isn’t doing much to fix it.’ 2020. Last accessed: June 2021
- Dow Jones. ‘Hi honey. I’m not from home.’ Last accessed: June 2021
- Apiservices.biz. ‘Copa-Cogeca Position Paper on the European Honey Market.’ February 2020. Available at: Copa-Cogeca position paper on the European honey market (apiservices.biz)
- WIRED. ‘The honey detectives are closing in on China’s shady syrup swindlers’. 2021. Last accessed: June 2021
- The Guardian. ‘US beekeepers sue over imports of Asian fake honey’. 2021. Last accessed: June 2021
- Times Live. ‘Falsely labelled, mixed with syrup or ‘laundered’: Honey fraud is rife in SA’. 2021. Last accessed: June 2021.
- UK Parliament Post. Postnote, number 624. ‘Food Fraud’. Last accessed: June 2021
- Agilent. ‘The Health Benefits of Honey’. 2017. Last accessed: June 2021
- Agilent. ‘Protecting our honey against food adulteration’. Last accessed: June 2021.